In contrast to traditional blockchains that depend heavily on hash power competition and hardware investment, this model responds to the high barriers that often prevent ordinary users from participating.
Looking at Pi Network through the lenses of system structure, consensus mechanism, role distribution, and security logic helps clarify how it functions and how it fundamentally differs from mainstream blockchain approaches.
What You Need to Understand Before Examining Pi Network’s Mechanism
To understand how Pi Network works, it is important to first recognize that it was not designed to be “fully decentralized from start”.
Most public blockchains emphasize permissionless access, hash power competition, and censorship resistance at launch. Pi Network took a different route. It began by lowering participation barriers to rapidly grow its user base, then gradually introduced a more complete blockchain structure. As a result, its system design clearly reflects a phased development strategy.
Under this framework, certain mechanisms in the early stages lean more toward coordinated management rather than full autonomy. This does not negate the goal of decentralization. Instead, it represents a trade off among network launch costs, user education, and technical complexity.
Pi Network’s Overall Operational Framework and System Architecture
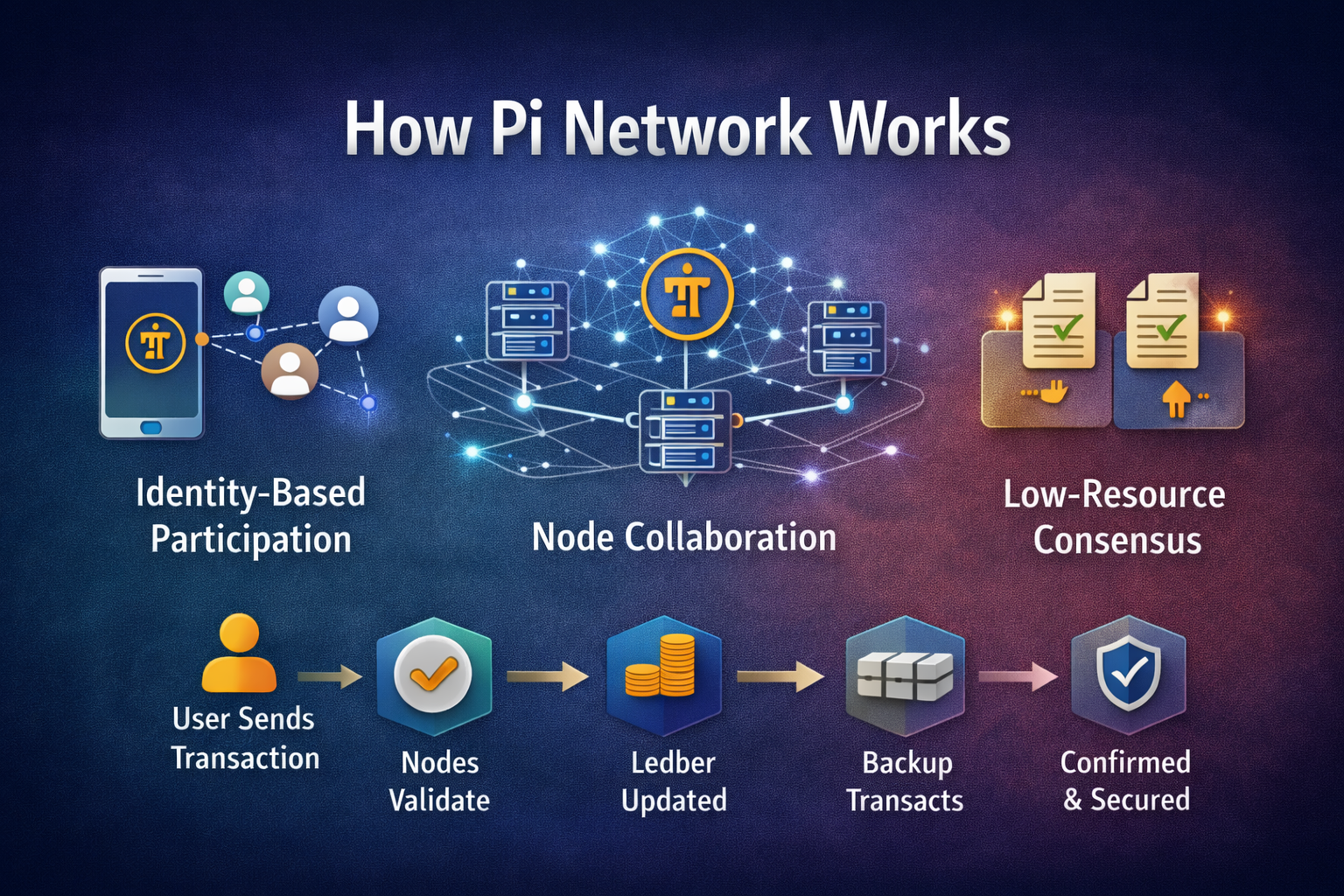
From an architectural perspective, Pi Network is not a single layer blockchain system. It operates through multiple functional layers working together.
User interaction layer: Implemented primarily through a mobile application, this layer handles identity binding, participation tracking, and basic operations. Its core focus is usability and a low technical threshold.
Network coordination layer: This layer connects users, nodes, and protocol rules, ensuring that participation activities are consistently recognized and integrated into system logic.
Blockchain and node network: This layer is responsible for maintaining the ledger, confirming transactions, and preserving state consistency.
This layered architecture allows Pi Network to run core functions even before the user base fully matures, while also leaving room for future system evolution.
How Pi Network’s Consensus Mechanism Is Established
Pi Network adopts the “Stellar Consensus Protocol (SCP)”, as its consensus mechanism. SCP was designed by Stanford professor David Mazières to improve transaction processing speed while maintaining security. Unlike the proof-of-work (PoW) or proof-of-stake (PoS) mechanisms of Bitcoin or Ethereum, SCP enables nodes to reach consensus without requiring significant computational resources.
Within Pi Network, SCP is implemented through the creation of “Security Circles”. These are trust based networks formed by users, where each person adds trusted individuals to their own circle. These overlapping circles collectively build the trust foundation of the entire network, helping ensure transaction authenticity and security.
Pi Network’s consensus model does not rely on computational work. Instead, it is built around identity verification, trust relationships, and node collaboration. The system emphasizes participant uniqueness and long term behavioral records, using trust networks to reduce the risk of Sybil attacks. On this foundation, node operators jointly validate transactions and maintain the ledger.
At its core, this approach replaces “resource consumption” with “social relationships and behavioral consistency”, significantly lowering energy costs.
While this gives Pi Network advantages in energy efficiency and scalability, it also places higher demands on identity verification mechanisms and node governance.
How PI’s Mobile Mining Mechanism Functions Within the System
Pi Network’s mining process differs significantly from traditional cryptocurrency mining. Users do not need to purchase expensive hardware or consume large amounts of electricity. Instead, participation involves the following steps:
Daily check in: Every 24 hours, users open the Pi Network app and tap the mining button to confirm their activity. This process uses minimal resources and does not drain the phone’s battery.
Building a Security Circle: After becoming a Pioneer, a user can become a Contributor by adding trusted friends or family members to their Security Circle. Each circle must include at least three to five members, which strengthens overall network security.
Inviting new users: As Ambassadors, users can share invitation codes to bring new participants into Pi Network. When a new user registers and begins mining, the inviter receives additional mining rewards.
From an operational standpoint, this mechanism serves as “proof of participation” rather than “proof of security”. It plays a central role in Pi Network’s cold start strategy.
Role Distribution and Collaboration Within Pi Network
Pi Network relies on the collaboration of multiple participant roles rather than a single controlling entity. Within its ecosystem, participants are divided into four role types:
Pioneer: The most basic role. Pioneers use their mobile devices to tap the “mine” button daily, confirming activity. They represent the main body of participants, and their engagement directly affects Pi token issuance.
Contributor: After becoming a Pioneer, a user can upgrade to Contributor by building a Security Circle and adding trusted members, thereby enhancing network security.
Ambassador: Ambassadors focus on promoting Pi Network and inviting new users. When someone joins through an Ambassador’s referral code and begins mining, the Ambassador receives rewards.
Node: Nodes are users who run Pi Network node software on their computers. They validate transactions, maintain blockchain integrity, and coordinate with the mobile application.
These four roles work together to support and expand the Pi Network ecosystem. This division of responsibilities allows open participation while gradually introducing more specialized maintenance capabilities to sustain long term operation.
How Transaction Confirmation, Ledger Maintenance, and Network Security Are Achieved
At the transaction processing layer, Pi Network relies on node collaboration to validate transactions and update the ledger.
Transactions must be confirmed by nodes before being recorded, and ledger consistency is maintained through consensus rules and node communication. Network security depends more on identity verification, node distribution, and rule enforcement than on computational barriers alone.
This structure is more resource efficient, but it also requires sufficient node decentralization and effective rule enforcement to mitigate centralization risks.
Challenges Facing Pi Network from an Operational Perspective
From a structural standpoint, Pi Network’s primary challenges lie in managing its transitional phases.
As the user base expands, the system must strengthen node decentralization and improve resistance to attacks, both of which present significant technical challenges.
In addition, moving from coordinated management to a fully autonomous network raises the bar for governance mechanisms, protocol upgrades, and consensus stability.
These challenges are not unique to Pi Network. They are common among crypto networks that follow a “users first, full on chain implementation later” development path.
Conclusion
Pi Network’s operational design reflects a user centered approach that gradually builds out blockchain functionality.
Through layered architecture, non computational consensus, and behavior driven incentives, the system seeks to balance low entry barriers with network security.
Understanding Pi Network from a structural perspective makes it possible to move beyond simplistic comparisons and develop a more rational view of its positioning and development path.
Related Articles
AI-Native Settlement Layers: How United Stables Is Building the Next Financial Rail
DePIN Identity Network and Real World Applications: How Humanity Protocol Brings on-chain Identity Into the Physical World
The ve(3,3) Flywheel Explained: How AERO Tokenomics Powers Aerodrome’s DeFi Economy
Aerodrome Tokenomics: How ve(3,3) Powers Base's Most Profitable DEX
Aster vs Hyperliquid: Which Perp DEX Will Prevail?