USR Stablecoin Loses Peg and Crashes 97%! Resolv Minting Vulnerability Leads to $25 Million Theft

At 2:21 a.m. UTC on Sunday, the attacker exploited a control vulnerability in the USR minting contract of the Resolv stablecoin protocol to mint over 80 million uncollateralized tokens with approximately $200,000 USDC, and stole about $25 million worth of assets by exchanging on exchanges. USR immediately plummeted to $0.025 in Curve Finance’s main liquidity pool.
Attack Mechanism: How the Minting Contract Was Exploited
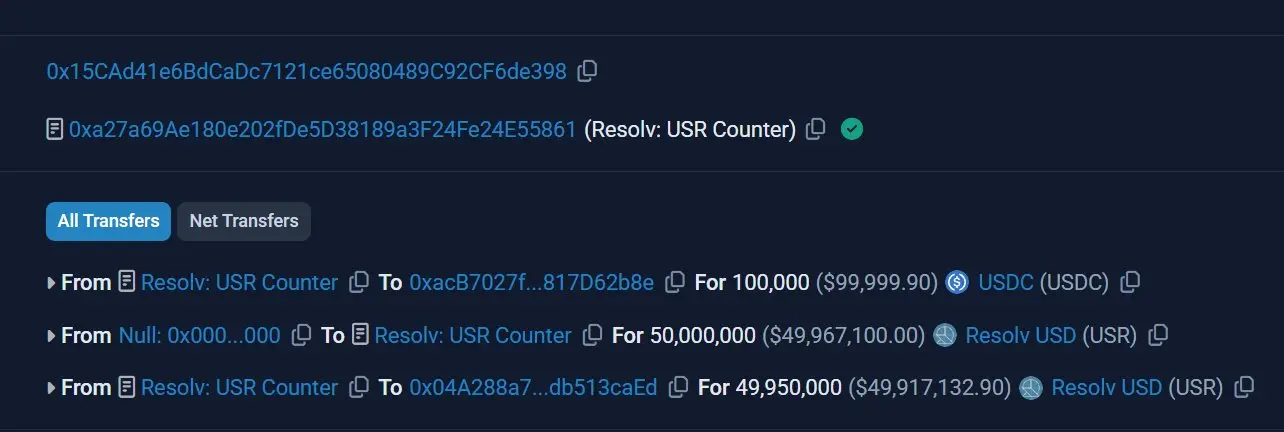
(Source: Etherscan)
Account YieldsAndMore first recorded this abnormal transaction: the attacker deposited 100,000 USDC into Resolv’s USR Counter contract and received 50 million USR, about 500 times the normal amount; then, through a second transaction, they minted an additional 300 million USR, totaling approximately 80 million tokens.
On-chain analyst Andrew Hong traced the root cause of the vulnerability to the protocol’s SERVICE_ROLE privilege. This role is used to fulfill exchange requests but is controlled only by a regular external account (EOA), not a more secure multi-signature setup. Additionally, the minting contract lacked oracle price verification, quantity limits, and minting caps.
DeFi fund D2 Finance proposed three possible attack vectors: oracle manipulation, compromise of off-chain signers, or missing quantity verification between mint requests and execution.
Market Impact: De-pegging Spreads to DeFi Lending Ecosystem

(Source: Trading View)
Within 17 minutes of the minting, USR in Curve Finance’s liquidity pool collapsed to $0.025, then rebounded to about $0.85 but did not fully regain its peg. The attacker’s main address (starting with 0x04A2) ultimately held 11,409 ETH (about $23.7 million), and another related address held approximately $1.1 million worth of wstUSR tokens.
Chain Reaction of USR De-pegging
Lending platform liquidity damage: USR and wstUSR are accepted as collateral by Morpho and Gauntlet. After de-pegging, some speculators bought USR at a discount and lent out USDC at face value, accelerating liquidity depletion in the vaults.
RLP insurance layer pressure: The Resolv liquidity pool (RLP), serving as a loss absorption mechanism, had about $38.6 million in circulating funds before the attack; the largest holder, Stream Finance, held 13.6 million RLP tokens on Morpho, with a net exposure of about $17 million.
RESOLV governance token decline: The event caused RESOLV to drop approximately 8.5% within 24 hours.
Although Resolv Labs claimed the collateral pools were “completely intact,” on-chain analysts pointed out that the attack was essentially an inflation of supply rather than a direct theft of collateral. The 80 million new tokens diluted existing circulation, and the attacker’s sell-off destroyed liquidity, causing substantial losses for users holding USR during the attack.
Limitations of Security Audits and Regulatory Intersection
Cyvers CEO Deddy Lavid stated: “Relying solely on audits is not enough; without real-time monitoring of minting and supply, you’re like a blind person at the most critical moment.” Resolv’s official website claims to have completed 14 audits from five firms and established a $500,000 bug bounty program through Immunefi.
The timing of this incident is sensitive. U.S. legislative bodies are actively advancing regulation of yield-bearing stablecoins under the GENIUS Act. Several key senators had already reached a principled agreement on stablecoin yield handling the day before the attack. Additionally, according to Immunefi’s latest report, the average loss from crypto attacks in 2026 is about $25 million, aligning with this incident’s amount and industry averages.
FAQs
What type of stablecoin is USR, and why did it de-peg?
USR is a USD-pegged stablecoin issued by Resolv Labs, employing a delta-neutral hedging strategy with ETH and BTC as underlying collateral. The de-peg was not due to insufficient collateral but resulted from an attacker exploiting a minting vulnerability to create large amounts of uncollateralized tokens and sell them on the market, causing the main liquidity pool to collapse instantly.
What is the core technical vulnerability of this attack?
The vulnerability lies in the control of the SERVICE_ROLE privilege account by a regular EOA, and the minting contract lacking oracle price checks, quantity verification, and minting caps. This allowed the attacker to mint USR tokens worth about 500 times the USDC they spent, with only around $200,000 USDC.
What are the actual risks for USR holders?
The attacker’s massive sell-off of uncollateralized USR directly destroyed liquidity. Users holding USR during the attack faced immediate market value losses. Additionally, wstUSR is used as collateral across multiple DeFi lending platforms, and the de-pegging effect further impacted the liquidity structure of related vaults.