Scallop’s abandoned V2 contract was exploited; after 150k SUI were stolen, it announced full reimbursement

Sui Network decentralized lending protocol Scallop, on April 26 (Sunday), released an official announcement via the X platform confirming that it suffered a vulnerability attack. The attacker extracted about 150,000 SUI from a discarded rewards contract associated with the sSUI spool. According to the official statement, the core liquidity pool and user deposits were not affected. The protocol has resumed deposits and withdrawals, and it confirms it will fully compensate all losses with company funds.
Event timeline and Scallop’s official response
According to Scallop’s official X platform announcement (April 26 at 12:50 UTC), the attack target was an affiliated incentive contract for the sSUI spool. This contract is the incentive layer for SUI depositors and is not the core lending logic. Within minutes after the incident, the Scallop team froze the affected contracts. The core contracts were frozen until they were unfrozen within two hours, and withdrawals and deposits resumed at 14:42 UTC.
Scallop’s official statement says: “Scallop will fully make up 100% of the losses.”
Vulnerability technical analysis: the uninitialized counter in the 2023 abandoned package
(Source: Vadim)
According to independent on-chain analysis, the attack entry point was the discarded V2 spool package deployed by Scallop in November 2023, more than 17 months before this attack occurred. Under Sui Network’s technical architecture, deployed packages cannot be changed; unless version control is explicitly set, old versions can still be called.
The attacker identified an uninitialized last_index counter in the package. This counter is used to track the accumulated rewards of stakers. The attacker staked about 136,000 sSUI; the system treated this position as one that had been in existence since the spool started in August 2023. After about 20 months of exponential accumulation, the spool index grew to about 1.19 billion, enabling the attacker to obtain about 162 trillion reward points, which they exchanged for 150,000 SUI in a 1:1 ratio.
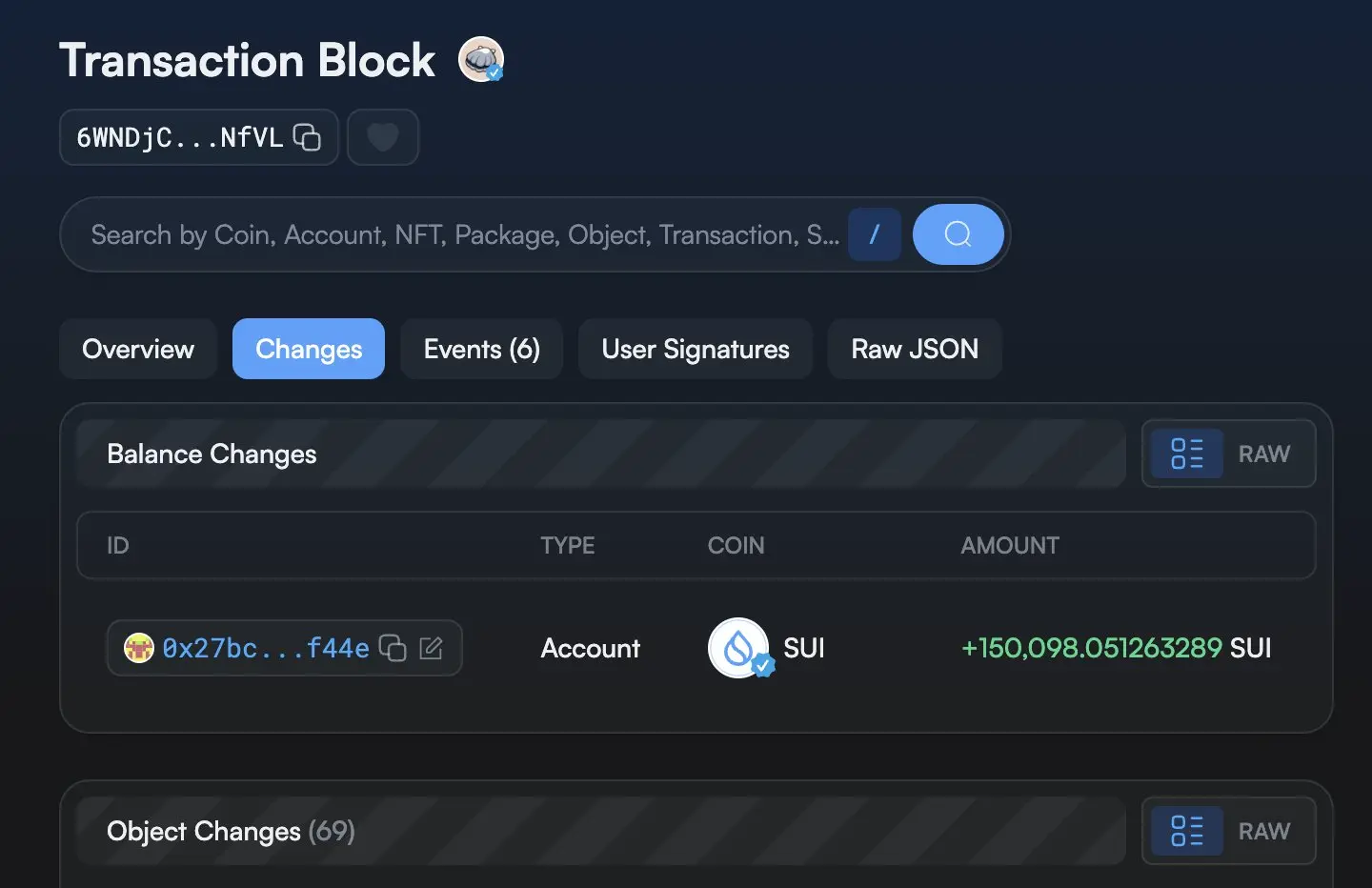
The on-chain transaction record can be looked up by hash: 6WNDjCX3W852hipq6yrHhpUaSFHSPWfTxuLKaQkgNfVL
Recent DeFi vulnerability incident records on Sui
According to public reports, in early April 2026, the Volo Protocol on Sui Network suffered a similar attack. The attack target was also an affiliated contract rather than core protocol logic, with losses of about $3.5 million. In addition, about a week before that attack, an Ethereum network bridge attack occurred in which about $292 million in unsecured liquidity re-staking tokens were stolen.
As of the time this report was published, both the Sui Foundation and Mysten Labs had not issued any public statements regarding the Scallop incident. According to Scallop’s official explanation, the protocol plans to conduct a comprehensive audit of all existing old-version packages; the audit timeline is yet to be determined.
FAQ
When did this vulnerability attack occur, and what was the scale of the losses?
According to Scallop’s official X platform announcement, the attack took place on April 26, 2026 (Sunday) at 12:50 UTC. The attacker extracted about 150,000 SUI from the abandoned sSUI spool incentive contract. The core lending liquidity pool and user deposits in other markets were not affected.
What official commitments did Scallop make regarding this attack?
According to Scallop’s official statement, the protocol froze the affected contracts within minutes after the attack and restored full operational functionality at 14:42 UTC (about two hours after the announcement was published). Scallop confirmed it would fully compensate all losses with company funds, that user earnings would not be affected, and that it plans to conduct a comprehensive audit of all existing old-version packages.
What was the root technical cause of this vulnerability, and how is it related to Sui Network’s technical architecture?
According to independent on-chain analysis, the vulnerability stemmed from an uninitialized last_index counter in a discarded V2 spool package deployed in November 2023. On Sui Network, deployed packages are immutable; unless version control is explicitly set, old versions can still be called. This allowed the attacker to exploit abandoned code from more than 17 months earlier to extract 150,000 SUI.
Related Articles
Western Union Remittance Q1 earnings call confirms: USDPT stablecoin launches in early May
Justin Sun calls TRON the world’s first post-quantum attack-resistant network, with the mainnet going live in Q3 of 2026.
DeFi United’s crowdfunding campaign raises 102,000+ ETH, with AAVE rebounding to $100
Vcitychain DPoS Mainnet Goes Live with Self-Developed Consensus System
ApeCoin Transfers Game Control to Community as Blackbeard's Bounty Season 3 Concludes
FLOA Ecosystem Launches FloaClaw AI Suite With Multi-Scenario Skill Matrix