What is Phala Coin?

What Is Phala (PHA)?
Phala (PHA) refers to the native token of the Phala Network, a blockchain protocol focused on privacy-preserving computation. The network enables a wide range of computational tasks without exposing original data, using privacy computing—a process where encrypted or protected data is processed, outputting only necessary results while keeping the underlying data confidential. PHA is used within the Phala ecosystem for paying for computation and service fees, staking as a validator or worker node, participating in governance voting, and more.
What Are the Current Price, Market Cap, and Circulating Supply of Phala (PHA)?
As of January 15, 2026, the real-time price, total market capitalization, and circulating supply of PHA can be found on CoinMarketCap and the Gate.com market pages (Source: CoinMarketCap, 2026-01-15). The privacy computing sector's value typically fluctuates based on overall market sentiment, Polkadot ecosystem growth, and real-world adoption.
Phala's maximum supply is commonly set at 1 billion tokens (Source: Phala documentation and public sources, July 2023), but circulating supply changes due to staking, unlocking schedules, and cross-chain liquidity. For precise figures before trading, review Gate.com's market page for “price”, “market cap”, and “circulating supply”, and assess recent 30-day volume and volatility to inform your trading strategy.
Who Created Phala (PHA), and When?
Phala Network was developed by a team using the Substrate framework to serve the Polkadot ecosystem. The project was initially deployed on the Kusama network as Khala before integrating into Polkadot’s parachain system (Source: Official announcements and community sources, 2021-2022). The team has consistently focused on privacy computing and Trusted Execution Environment (TEE) adoption, enhancing mainnet functionality, cross-chain interoperability, and developer tooling over time.
How Does Phala (PHA) Work?
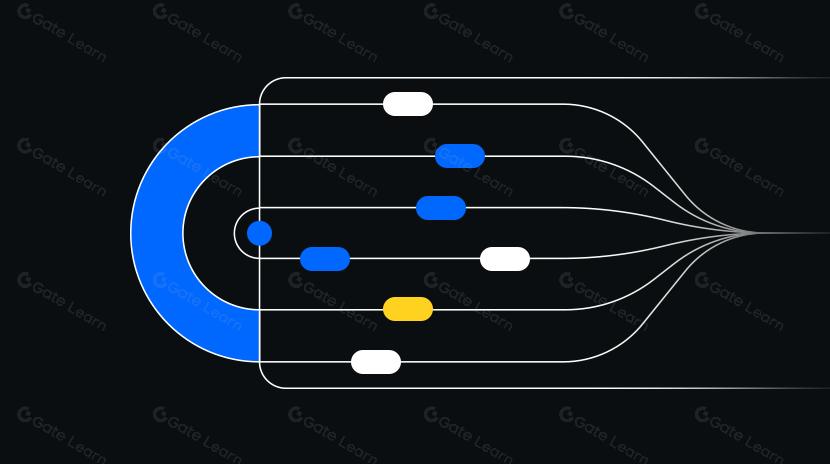
Phala’s architecture separates privacy computation from blockchain settlement and governance:
- Computation is performed in a Trusted Execution Environment (TEE), an isolated secure enclave within specific hardware that prevents external programs from accessing data or processes.
- Results are verified and settled on-chain. The blockchain records tasks, settles fees, manages governance and staking; off-chain TEE executes confidential computations. Both layers interact through protocol messaging to ensure auditability.
- Phala is interoperable with Polkadot’s parachains. A parachain operates in parallel within Polkadot’s shared security model, facilitating seamless cross-chain asset and resource transfers.
What Can You Do With Phala (PHA)?
- Pay for privacy-preserving computation tasks—e.g., running AI inference models without exposing training data.
- Stake PHA to participate in network security as a validator or worker node and earn rewards.
- Take part in governance by voting on upgrades and parameter changes.
- Developers and businesses can use Phala to build confidential DeFi modules, data marketplaces, or AI inference services—keeping user data private during operation.
Wallets and Extensions in the Phala (PHA) Ecosystem
For Polkadot ecosystem addresses, consider browser extension wallets such as Polkadot{.js}, Talisman, or SubWallet—these support parachain accounts and dApp authorizations. Hardware wallets like Ledger add an extra layer of offline private key protection when compatible apps are available. Your private key represents ownership of your assets—never share it; mnemonic phrases are backup words for your private key—record them offline and store securely. For cross-chain bridges or multi-chain deployments (e.g., ERC-20 versions), verify target chains and contract addresses before transferring to prevent sending assets to incompatible addresses.
Main Risks and Regulatory Considerations for Phala (PHA)
- Price and Liquidity Risks: Crypto assets are volatile; order depth and slippage can affect transaction outcomes.
- Technical and Supply Chain Risks: TEE depends on hardware security—monitor disclosures about side-channel attacks or supply chain vulnerabilities.
- Cross-chain & Compliance Risks: Smart contract errors or operational mistakes in bridges/multi-chain assets can cause losses; different jurisdictions have compliance requirements regarding privacy tech and data handling—research these ahead of time.
- Private Key Management Risks: Leaked private keys or mnemonic phrases result in irreversible asset loss. Use two-factor authentication, withdrawal whitelists, and hardware wallets for enhanced security.
How to Buy and Safely Store Phala (PHA) on Gate.com
Step 1: Register and Complete KYC. Sign up on Gate.com’s official site and follow identity verification prompts to increase limits and security.
Step 2: Deposit Funds. On the asset page, choose fiat deposit or crypto recharge. If depositing USDT or similar tokens, confirm that your selected network (e.g., ERC-20) matches your withdrawal network to avoid errors.
Step 3: Place a Buy Order. On the trading page, search “PHA” and select your preferred pair (such as PHA/USDT). You can use limit orders to specify price or market orders for immediate execution at current prices.
Step 4: Withdraw to a Wallet. For long-term holding or ecosystem participation, go to the withdrawal page:
- For Polkadot ecosystem addresses, use a compatible parachain wallet and test with a small amount first.
- For ERC-20 addresses, ensure contract and network are “ERC-20”. Any mismatch between chain and address can result in asset loss.
Step 5: Secure Storage. Enable two-factor authentication on your account, set withdrawal whitelists; record your mnemonic phrase offline in a fireproof/waterproof location; use hardware wallets for additional private key security if possible.
Comparison: Phala (PHA) vs Oasis (ROSE)
Positioning & Ecosystem: Both target privacy computing; Phala is deeply integrated into Polkadot’s parachain ecosystem, while Oasis focuses on its own mainnet with ParaTimes architecture supporting confidential smart contracts. Technical Approach: Phala emphasizes TEE hardware execution with layered on-chain settlement; Oasis also supports confidential computation but differs in execution environments and architecture. Token Utility: PHA is used for computation payments, staking, and governance; ROSE serves similar fee/staking functions but differs in economic model and incentives. Application Focus: Both aim at data economy, privacy DeFi/AI use cases. Differences often appear in developer tooling, cross-chain interoperability, and the number of deployed projects in their respective ecosystems.
What Is the Long-Term Value Proposition of Phala (PHA)?
Combining privacy and computational power is foundational for Web3 and the data economy. With rising regulatory demands for compliant AI inference, healthcare, finance, and other sensitive sectors, networks that provide auditable results without revealing underlying data offer significant utility. Phala’s integration of TEE with on-chain settlement—leveraging Polkadot’s shared security and cross-chain capabilities—positions it well for multi-chain enterprise applications. Long-term value depends on adoption rates, developer ecosystem activity, hardware security advancements, and governance effectiveness.
Summary of Phala (PHA)
Phala (PHA) underpins both economic transactions and governance within a privacy computing network designed for secure operations in TEEs, on-chain settlement, and cross-chain interoperability. For market activity, always check Gate.com and public data sources for up-to-date prices, market caps, and supply before trading; operationally, match deposit/withdrawal networks and addresses with small-scale tests and robust security practices; in terms of value proposition, focus on real-world adoption, ecosystem tooling maturity, and progress in Polkadot interoperability. For everyday users, start small with stepwise practice—adjust positions according to risk tolerance and understanding of privacy computing trends.
FAQ
Is PHA Suitable for Beginner Investors?
PHA is a project token within the privacy computing sector—ideal for those interested in Web3 privacy technologies. Newcomers should thoroughly research project fundamentals, market risks, and personal risk tolerance before investing; start with small amounts. Buying through regulated exchanges like Gate.com and safeguarding private keys are essential for protecting your assets.
What Are the Practical Applications of Privacy Computing on Phala Network?
Phala leverages Trusted Execution Environment (TEE) technology to deliver on-chain privacy-preserving computation—applicable in DeFi private transactions, personal data protection, and enterprise-grade privacy scenarios. User data remains encrypted during processing so third parties cannot access it—critical for sensitive fields like finance or healthcare.
What Is PHA’s Supply Model and Inflation Mechanism?
PHA has a total supply of 100 million tokens with a gradual unlocking mechanism. New PHA rewards are distributed via mining and staking on the Phala Network—the primary source of token inflation. Understanding unlock schedules and circulating supply trends helps assess long-term investment value.
What Are the Staking Rewards in the Phala Ecosystem?
Staking PHA on Phala Network yields block rewards plus transaction fee sharing. Stakers act as network validators—securing privacy computation while earning ongoing returns. Different staking methods (direct staking vs delegated staking) offer varying yields; beginners should consult Gate.com or official wallet resources for current rates.
How to Evaluate Phala Project’s Prospects?
Assess through several dimensions: number/activity of ecosystem apps (DeFi, data services), technical innovation (TEE integration depth, scalability), market recognition (exchange listings, community size), team background/funding status. Follow official updates for an objective view of development potential.
Key Terms Related to Phala (PHA)
- TEE (Trusted Execution Environment): An isolated secure area within hardware used for tamper-resistant processing of sensitive data and smart contracts.
- Privacy Computing: On-chain computation that preserves user data confidentiality—a core technical feature of Phala.
- Worker Node: Network participant running TEE-enabled hardware to execute confidential smart contracts in exchange for rewards.
- Smart Contract: Automated program on Phala Network executing business logic with privacy guarantees inside TEE environments.
- Substrate: The modular blockchain framework underpinning Phala—enabling scalable governance and extensibility.
- Cross-chain Interoperability: Phala’s ability to exchange data/value across blockchains via relay chains.
References & Further Reading
-
Official Website/Whitepaper:
-
Development/Documentation:
-
Media/Research:
Related Articles

In-depth Explanation of Yala: Building a Modular DeFi Yield Aggregator with $YU Stablecoin as a Medium
Exploring 8 Major DEX Aggregators: Engines Driving Efficiency and Liquidity in the Crypto Market
