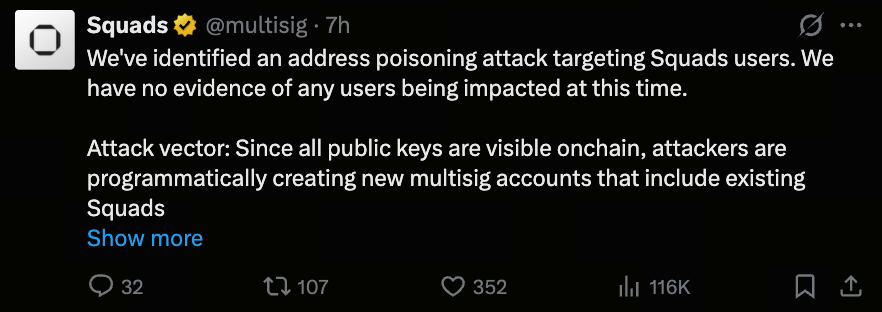
Squads Users Alert: Understanding Address Poisoning Attacks and How to Stay Safe
What Is an Address Poisoning Attack?
In the blockchain space, an address is fundamentally a publicly visible string, which means anyone can observe and leverage this information to design attacks.
The recent incident targeting Squads users is a classic example of address poisoning. Attackers create fake addresses that closely resemble your account, using visual deception to prompt mistaken actions. This type of attack does not compromise the system directly—it exploits human error in judgment.
How Does the Attack Occur?
(Source: multisig)
This event primarily unfolded through two methods:
- Forging Multisig Accounts
Attackers set up new multisig wallets and add the victim’s public key to the member list, causing these accounts to appear in the user interface. Because the system displays accounts associated with your address, these fake accounts blend into your list.
- Imitating Address Formats
Attackers intentionally generate addresses with beginnings and endings similar to legitimate ones. For example:
-
Real address: ABCD...XYZ
-
Fake address: ABCF...XYA
If you only check the first and last few characters, it’s easy to misjudge.
What Is the Purpose of the Attack?
The main objective of this attack isn’t to hack systems, but to trick you into making mistakes.
Common goals include:
-
Accidentally transferring funds to a fake address
-
Signing transactions you did not initiate
-
Mistaking fake accounts for team accounts
The errors stem from user actions, not system vulnerabilities.
Is Fund Security Affected?
Currently, the key takeaway is that there have been no known fund losses, and the protocol itself remains uncompromised.
Attackers cannot:
-
Access your assets
-
Modify your multisig settings
-
Force transactions to execute
As long as you avoid operational mistakes, your assets remain secure.
Official Upcoming Security Updates

(Source: multisig)
To further mitigate risk, the Squads team has planned a series of UI enhancements:
- Short Term (Immediate)
-
Display security warning banners
-
Mark multisig accounts that have never interacted before
- Mid-Term (Within a Few Days)
-
New accounts will default to a pending confirmation status
-
Users must manually add accounts to their list (whitelist mechanism)
The core objective of these features is to reduce the likelihood of mistaking addresses.
How Should Users Protect Themselves?
To mitigate potential attack risks, it’s essential to develop sound operational habits. Always remain vigilant with unfamiliar multisig accounts—only interact with accounts you created or those explicitly verified by your team. Avoid engaging with suspicious addresses, and never rely solely on the first or last few characters to verify authenticity. The best practice is to compare the full address or confirm through internal records and whitelists to minimize errors.
In addition, since multisig environments typically involve multiple collaborators, any uncertain transaction should be confirmed with the team before proceeding to prevent asset loss due to miscommunication. It’s also recommended to pin frequently used and trusted accounts to the top of your list—this not only boosts efficiency but also reduces the risk of accidental clicks or mistakes.
Summary
Address poisoning attacks are fundamentally a form of social engineering that exploits human nature, not technical flaws. The Squads case is a strong reminder that blockchain security relies not just on protocol design, but also on user behavior. In the on-chain world, consistently verifying addresses and carefully signing transactions are the most important defenses for protecting your assets.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


