Ethereum 2026: Vitalik’s Bet on Trustlessness
For the past decade, Ethereum made calculated compromises. It traded trustlessness for convenience, self-sovereignty for user experience, and decentralization for mainstream adoption.
Every time you check your wallet balance, you trust companies like Alchemy or Infura. Every time you use a dapp, your data is leaked to servers you never chose.
But 2026 marks an inflection point. This is the year Ethereum stops asking, whether it is worth diluting ourselves for mainstream adoption. The answer is – no longer.
The vision:
- Full nodes easy to run again (ZK-EVMs + Block-Level Access Lists)
- Verifiable RPCs instead of blind trust (Helios light client)
- Private payments with public payment UX
- Wallets beyond fragile seedphrases (social recovery)
- Unstoppable dapp UIs (IPFS hosting)
- Censorship-resistant block building (FOCIL)
The Backsliding: How we got here
Ethereum’s infrastructure became increasingly centralized even as the base layer stayed decentralized.
Nodes went from laptop-friendly to requiring 800+ GB storage and 24-hour syncs. Dapps evolved from simple HTML pages into server-side monsters leaking your data everywhere. Wallets shifted from user-controlled RPCs to hardcoded providers tracking everything you do.
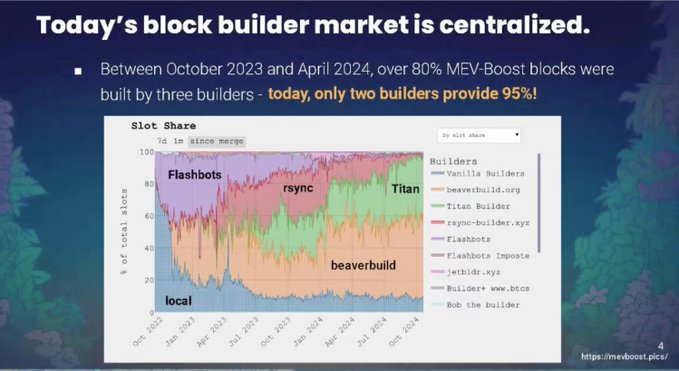
Most dramatically, 80-90% of Ethereum blocks are now produced by just 2 builders. This concentration puts transaction inclusion under control of a handful of entities who can censor whatever they want.
These weren’t mistakes, they were pragmatic choices made while scaling under Proof of Work constraints.
But the cost was real: trust assumptions crept into “trustless” systems, single points of failure proliferated, and users lost genuine self-sovereignty. We decentralized the ledger but re-centralized the access layer.
The 2026 Vision: Seven Pillars
1. Full Nodes
Today’s reality: 800+ GB storage, 24-hour sync, constant uptime needed. Most users gave up.
Block-Level Access Lists (BAL) change this fundamentally. Think of BALs as a table of contents for each block, it tells you upfront exactly which state the block will touch. Your computer prefetches everything in parallel before execution starts. Transactions that don’t conflict run simultaneously on separate cores. Analysis shows 60-80% of transactions have no overlap.
Combined with ZK-proofs that verify blocks without re-executing everything, sync times drop dramatically and storage becomes manageable. Running a node transitions from “infrastructure companies only” back to “decent laptop territory.”
2. Helios: Verify your RPC
Picture this attack: You’re swapping on Uniswap. Your malicious RPC shows you a fake price. You sign accepting fewer tokens than you should. The RPC executes a sandwich attack and keeps the profit. You never see it coming.
This hasn’t happened with major providers but it’s technically possible. The problem: you’re trusting someone else to tell you the blockchain state.
Helios solves this in 2 seconds. It’s a light client that tracks validator “sync committees” (512 validators, ~27 hour periods). If 2/3+ sign a block header, it’s canonical. When you check your balance, Helios requests a Merkle proof from the untrusted RPC and verifies it locally. The RPC can refuse to answer but cannot lie.
It runs anywhere: laptop, phone, browser extensions. Use it as your MetaMask RPC and every dapp becomes trustless without changing anything else.
The tech exists today, open source and ready for integration.
3. ORAM & PIR: Private Queries
Every RPC query leaks your behavior, which addresses you watch, protocols you use, when you use them.
ORAM (Oblivious RAM) hides access patterns using tree structures. The server sees you accessing data but can’t tell which data. Signal messenger uses this, it cuts their costs 100x (from 500 servers to 6).
PIR (Private Information Retrieval) lets you query databases without revealing what you want. You send an encrypted query, the server processes it on encrypted data, and you decrypt the answer. Response sizes stay constant (~3KB) regardless of database size.
Real implementations exist today:
- Oblivious Labs: Private WBTC balance checker
- sprl.it: Private ENS resolution
- QuietRPC: Private RPC exploration
The challenge is dynamic state: re-encoding 33M elements takes 4-20 minutes. The solution involves periodic snapshots with on-chain attestation. For most uses (balance checks, voting eligibility), a few minutes staleness is acceptable for the privacy guarantee.
4. Social Recovery: Beyond Seedphrases
Current wallets force impossible choices:
- Lose seedphrase → lose everything
- Seedphrase stolen → lose everything
- Cloud backup → sovereignty backdoored
Social recovery distributes trust. You have a daily signing key plus “guardians” (friends, family, other devices). Recovery requires 3-of-5 guardians approving. Timelocks (48-72 hours) prevent instant theft while allowing legitimate recovery.
Drop your phone in a lake? Contact guardians, they approve a new key, timelock starts, you regain access. If someone stole your key and tries this, you cancel during the timelock.
Security: attackers need 3-of-5 guardians simultaneously. You have days to respond. Each guardian has partial power only. No tech company backdoors.
Wallets like @ ready_co and @ Safe support this today. The 2026 goal: make it standard everywhere with UX anyone can use.
5. Private Payments as Default
Privacy tools exist but are painful: different apps, terrible UX, 3-5x gas costs, limited support. Almost nobody uses them.
2026 goal: private = public experience. Same wallet, same interface, comparable costs. Privacy becomes a checkbox, not a research project.
Technologies: zkSNARKs (prove you have funds without revealing which), stealth addresses (one-time addresses per transaction), Account Abstraction integration.

6. FOCIL: Censorship-Resistant Privacy
Private payments are worthless if builders refuse to include them. With 80-90% of blocks from 2 builders, censorship is trivial.
FOCIL (Fork-Choice enforced Inclusion Lists) makes censorship impossible:
Each slot, 16 validators randomly selected build “inclusion lists” (8KB each) from mempool transactions. Block builders must include these transactions. Attesters only vote for blocks that satisfy inclusion lists. Without votes, blocks can’t become canonical.
Why it works:
- Committee-based: only needs 1-of-16 honest validators
- Fork-choice enforced: built into consensus, can’t bypass
- Same-slot: no delays
- Anywhere-in-block: builders optimize MEV but can’t censor
For privacy: if one validator includes your private transaction, it must be in the block. Builders cannot censor without losing money.
7. IPFS-Hosted Dapps
When you visit app.uniswap.org, you’re loading a web app from their servers. If servers go down, you’re locked out. If hacked for one second, malicious UI drains your wallet. If pressured, they serve different UIs to different users.
IPFS solution: Host UIs using content addressing (identified by hash, not server). Anyone can serve content. Changing UI changes hash. ENS maps friendly names to hashes.
Benefits: no single point of failure, impossible to hijack, censorship resistant, verifiable.
Challenge: updates mean new hashes. Solution: ENS records point to the latest hash, progressive decentralization to DAO governance.
Why this matters
“In the world computer, there is no centralized overlord. There is no single point of failure. There is only love.” - Vitalik
If Ethereum becomes just another platform requiring trust in intermediaries, why not use AWS?
The answer must be that Ethereum offers something genuinely different: true ownership, real permissionlessness, actual censorship resistance, genuine self-sovereignty.
But these only matter if accessible. A theoretically decentralized system accessed through centralized chokepoints is just decentralization theater.
The stakes:
- Success: Ethereum becomes foundational infrastructure for an open internet, users control their wealth/data, privacy is default
- Failure: Regulatory capture at access layer, users abandon crypto for honest CBDCs, cypherpunk dream dies
The decade of pragmatism proved blockchains work. Now we prove they work without abandoning principles.
Conclusion
This won’t all ship next release. Building trustless systems with great UX takes time. Coordinating hundreds of developers takes longer.
But the commitment is absolute. Every decision evaluated against: does it increase trustlessness and self-sovereignty?
2026 is when we decided mainstream adoption at the cost of core values isn’t worth it. That “good enough” decentralization isn’t good enough. That users deserve better than trusting infrastructure providers to access “trustless” networks.
The technical pieces are falling into place. Helios provides verifiable RPC today. ORAM/PIR demonstrate private queries work. Social recovery exists in production. FOCIL’s censorship resistance is specified. The path is clear.
Now let Ethereum build.
Disclaimer:
- This article is reprinted from [stacy_muur]. All copyrights belong to the original author [stacy_muur]. If there are objections to this reprint, please contact the Gate Learn team, and they will handle it promptly.
- Liability Disclaimer: The views and opinions expressed in this article are solely those of the author and do not constitute any investment advice.
- Translations of the article into other languages are done by the Gate Learn team. Unless mentioned, copying, distributing, or plagiarizing the translated articles is prohibited.
Related Articles

What Is Ethereum 2.0? Understanding The Merge

Reflections on Ethereum Governance Following the 3074 Saga
Our Across Thesis

What is Neiro? All You Need to Know About NEIROETH in 2025

What is Polygon 2.0 (POL)? From MATIC to POL (2025)


