What is ZEROBASE (ZBT)? A comprehensive overview of its on-chain data infrastructure and decentralized computing model
In traditional Web3 architectures, data processing and computational power often depend on centralized services, making it challenging to ensure both transparency and privacy. ZEROBASE addresses this by leveraging zero-knowledge proofs and Trusted Execution Environments (TEE), enabling verifiable computations without exposing sensitive data and filling a critical gap in trustworthy on-chain data processing.
From a broader blockchain infrastructure perspective, ZEROBASE is more than a data processing network; it serves as a vital bridge connecting privacy computation, compliance requirements, and decentralized execution, providing foundational support for next-generation Web3 applications.
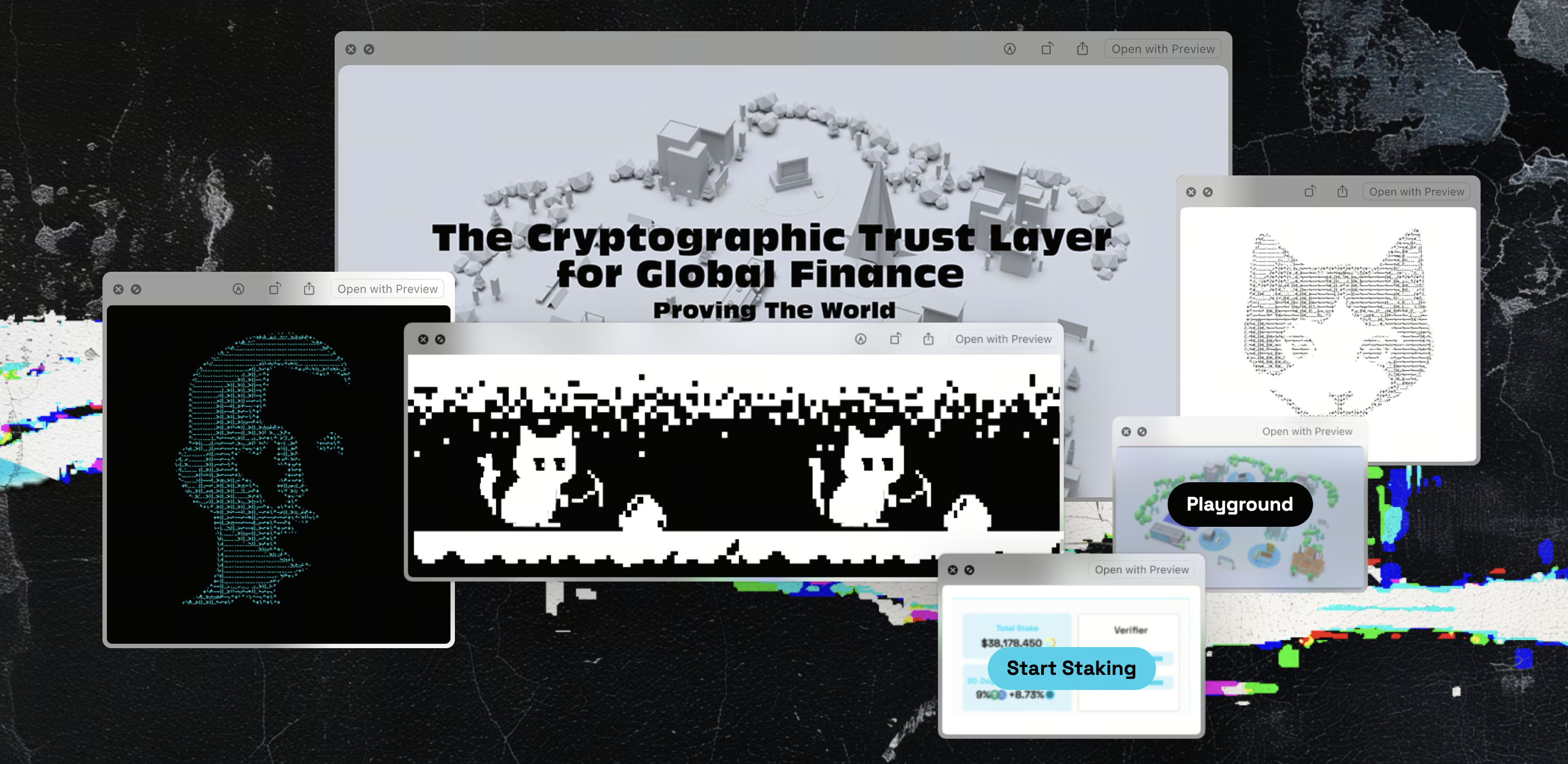
Source: zerobase.pro
What Is ZEROBASE
ZEROBASE is fundamentally designed as an infrastructure network that integrates both data processing and computational execution. Unlike protocols focused solely on data indexing or storage, ZEROBASE delivers dual functionality: processing data and verifying computations.
This network operates as a decentralized computation layer, specialized for executing complex tasks and generating verifiable results. Developers leverage this architecture to run off-chain computations and submit verifiable outcomes to the blockchain.
The synergy between the decentralized computation network and on-chain data infrastructure forms the core capability of ZEROBASE, enabling seamless workflows from data querying to advanced computation.
ZEROBASE Technical Architecture: Data Layer, Computation Layer, and Network Structure
ZEROBASE employs a multi-layer architecture, segmenting distinct functions into independent modules to maximize scalability and performance.
Its architecture consists of three primary layers:
-
Data Layer: Handles data input, processing, and structuring
-
Computation Layer: Executes tasks and produces zero-knowledge proofs
-
Network Layer: Coordinates nodes and manages task distribution
The HUB-Prover model orchestrates network coordination:
-
HUB nodes manage task scheduling and routing
-
Prover nodes execute computations and generate proofs
TEE (Trusted Execution Environment) ensures input data privacy, preventing exposure to node operators during processing.
This design delivers a blend of privacy, verifiability, and high performance, supporting large-scale computational requirements.
ZEROBASE Operating Mechanism: Data Processing and Computation Workflow
ZEROBASE operates through a standardized, task-driven workflow for data processing and computation. Its core approach decomposes complex computations and delegates them to a decentralized network, guaranteeing verifiable results.
Users or applications initiate data requests or computation tasks—ranging from on-chain analytics and privacy computations to complex logic processing. The network’s coordination layer (HUB nodes) schedules and assigns these tasks to appropriate Prover nodes. This distributed computation workflow enables scalable computational power.
During execution, Prover nodes complete assigned tasks and generate zero-knowledge proofs, validating the correctness of results without revealing original data. Data inputs are typically processed within a Trusted Execution Environment (TEE), minimizing the risk of data leakage.
Final computation results and proofs are returned for on-chain verification. This closed-loop structure—computation, proof, and verification—empowers ZEROBASE to deliver efficient computation while safeguarding privacy and trust.
ZBT Token Functionality: Incentives, Payments, and Network Security
ZBT is the core functional asset of the ZEROBASE network, underpinning resource access, incentive distribution, and security across the ecosystem.
For payments, ZBT serves as the network’s unit of account, used to pay for data processing and computation fees. Users spend ZBT when submitting tasks, establishing a market-driven supply and demand for computational resources.
For incentives, network participants—Prover nodes and coordination nodes—earn ZBT rewards for task completion. This mechanism ties returns directly to computational contributions, incentivizing nodes to consistently provide hash power and services. Staking mechanisms (such as stablecoin staking) further regulate node behavior and enhance execution reliability.
For security, ZBT maintains network stability through incentive and penalty systems. Nodes exhibiting abnormal behavior (e.g., failing tasks or submitting incorrect results) face reduced rewards or loss of staked assets, enforcing economic discipline. Collectively, ZBT creates an interconnected “use—incentive—constraint” economic model.
ZEROBASE Use Cases: From Data Services to AI and On-Chain Analytics
ZEROBASE’s architecture supports a broad spectrum of applications, from foundational data services to advanced computational scenarios—particularly those demanding privacy and verifiability.
At its core, ZEROBASE functions as an on-chain data processing network, enabling data querying, processing, and structuring for applications. These capabilities resemble Web3 data infrastructure, but with expanded computational functionality: beyond “reading data,” it also “processes data.”
In more advanced scenarios, decentralized computation powers AI model tasks, data analytics, and privacy-preserving computations. For example, when analyzing sensitive data without exposing originals, zero-knowledge proofs validate computational results, enabling “verifiable but invisible” data processing.
As a result, ZEROBASE delivers efficient, privacy-focused, and trustworthy solutions for financial analytics, on-chain behavior research, and compliance-driven data processing.
ZEROBASE vs. Other Data Protocols: The Graph / Filecoin Comparison
ZEROBASE is distinctly different from other Web3 data protocols in its functional approach.
The Graph specializes in data indexing and querying; Filecoin is dedicated to decentralized storage.
ZEROBASE, by contrast, prioritizes “computation + verification,” not just storage or indexing.
| Dimension | ZEROBASE | The Graph | Filecoin |
|---|---|---|---|
| Core Function | Data Processing + Computation | Data Indexing | Data Storage |
| Supports Computation | Yes | No | No |
| Privacy Capability | ZK + TEE | None | Limited |
| Main Use | Computation and Verification | Data Query | Data Storage |
This comparison underscores ZEROBASE’s positioning as decentralized computation infrastructure, rather than a single-purpose data protocol.
ZEROBASE Advantages, Limitations, and Common Misconceptions
ZEROBASE’s primary advantage is its ability to deliver both privacy protection and verifiable computation—an uncommon combination in conventional blockchain or data infrastructure. By integrating zero-knowledge proofs (ZK) and Trusted Execution Environments (TEE), ZEROBASE proves computational correctness without exposing original data, meeting stringent privacy and compliance requirements.
Its multi-layer architecture (data, computation, coordination) delivers robust scalability, supporting complex tasks and diverse applications. Distributed computation and task scheduling further optimize resource utilization and overall efficiency.
However, this design introduces some limitations. Zero-knowledge proofs are computationally intensive, potentially affecting performance in high-frequency or large-scale scenarios. The multi-role, multi-layer structure increases system complexity, raising development and participation barriers.
System performance also depends on node quality and network coordination. Instability in task scheduling or node performance can impact overall efficiency. A common misconception is viewing ZEROBASE as a “data storage network” or “data indexing protocol,” when its true value lies in computation and verification—not mere storage or querying.
Conclusion
ZEROBASE merges zero-knowledge proofs, decentralized computation, and on-chain verification to create innovative infrastructure for data processing and privacy computation. Its design focuses on establishing verifiable links between trustworthy computation and privacy protection, rather than replacing traditional data services.
The core value is verifiable computation: delivering auditable, trustworthy results without exposing sensitive data, expanding blockchain’s utility in data-intensive and compliance-driven environments.
Despite ongoing challenges in performance costs, system complexity, and participation thresholds, ZEROBASE presents a viable path for integrating privacy computation with on-chain verification, offering fresh design perspectives for Web3 infrastructure.
FAQ
- Is ZEROBASE a data protocol or a computation network?
It is primarily a decentralized computation network with integrated data processing capabilities.
- What is the purpose of the ZBT token?
It is used for computation payments, node incentives, and maintaining network operations.
- How does ZEROBASE differ from The Graph?
The Graph is focused on data indexing; ZEROBASE delivers computation and verification capabilities.
- How does ZEROBASE protect data privacy?
By utilizing zero-knowledge proofs and Trusted Execution Environments (TEE).
- Can ZEROBASE be used for AI computation?
Its architecture supports data processing and computational tasks, making it adaptable for AI scenarios.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


