What Is Umbra? How Closing Its Frontend Reflects the Tradeoff Between Hacker Risk and Openness
Event Overview: Why Did Umbra Suspend Its Service?
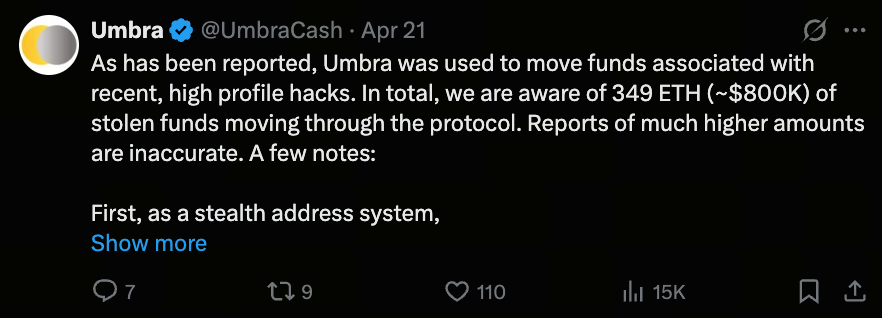
Umbra, a protocol focused on privacy protection, recently announced the temporary shutdown of its official front-end website. This decision was triggered by a series of hacking incidents: about $800,000 in suspicious funds were found to have been transferred through the protocol, with sources linked to several recent major attacks.
 (Source: UmbraCash)
(Source: UmbraCash)
To prevent ongoing abuse, the team placed the official entry point in maintenance mode and stated that the website would only be restored after confirming it would not interfere with fund recovery efforts.
Key Question: Can Shutting Down the Front-End Really Stop Hackers?
This event highlights a crucial fact: shutting down the website does not equal stopping protocol operations.
The reason lies in blockchain’s fundamental characteristics:
-
Once a Smart Contract is deployed, it typically cannot be shut down
-
Open-source front-ends can be redeployed by others
-
Users can still interact directly with on-chain contracts
Therefore, even if the official entry point is closed, it is technically impossible to fully block fund movement.
Background: Kelp Attack and Fund Transfers
This incident is closely tied to another major security breach. The decentralized protocol Kelp was recently hacked, resulting in losses exceeding $280 million. The market widely suspects a connection to North Korean hacker organizations.
Subsequent on-chain tracking showed:
-
Attackers attempted to transfer Assets through various protocols
-
Including converting funds from Ethereum to the Bitcoin network
-
Umbra was identified as one of the possible tools used
Umbra’s Position: Not a Money Laundering Tool
Umbra stresses that its design is not intended to conceal the source of funds, but to protect recipient privacy. Specifically, the protocol hides the receiving address, not the origin or flow of transactions; funds remain traceable. The team also noted that all suspicious funds passing through the protocol are still identifiable and have been analyzed in partnership with security researchers.
Technical Analysis: What Is a Stealth Address?
Umbra’s core technology is the Stealth Address, which works as follows:
1. Dynamic generation of receiving addresses
Each transaction creates a new temporary address.
2. Concealing recipient identity
External observers cannot directly link the transaction to the recipient’s main Wallet.
3. Exclusive identification by both parties
Only the sender and recipient can confirm the true counterpart of the transaction.
This design primarily addresses privacy concerns caused by excessive transparency on public blockchains.
Difference from Mixers: Why Is Regulatory Attitude Different?
Umbra is fundamentally different from tools like Tornado Cash:
-
Tornado Cash: Obscures sources by mixing funds
-
Umbra: Does not mix funds, only hides recipient information
As a result, Umbra is generally viewed as a compliance-friendly privacy tool.
Multi-Chain Development and Positioning: Umbra’s Role
 (Source: UmbraCash)
(Source: UmbraCash)
Umbra is not only deployed on Ethereum but is steadily expanding to other chains such as Solana, while continuously advancing privacy technology.
Its role can be seen as foundational privacy infrastructure within the DeFi ecosystem.
Recent developments include:
-
Integration of new cryptographic execution technologies
-
Support for more complex privacy transaction scenarios
Core Contradiction: Privacy vs Security
This event once again underscores a persistent challenge in the blockchain space: the dual nature of privacy tools. For retail investors, they protect personal information and Assets; for hackers, they may facilitate fund transfers. Protocol designers must balance user privacy, regulatory demands, and system openness.
Summary
Umbra’s decision to shut down its front-end demonstrates that even in a decentralized environment, teams take proactive steps to mitigate risk. At the same time, it reminds us that truly decentralized systems are difficult to shut down or control through any single action. Moving forward, the challenge for all blockchain privacy protocols will be preventing abuse without compromising privacy.
Related Articles

In-depth Explanation of Yala: Building a Modular DeFi Yield Aggregator with $YU Stablecoin as a Medium

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape


