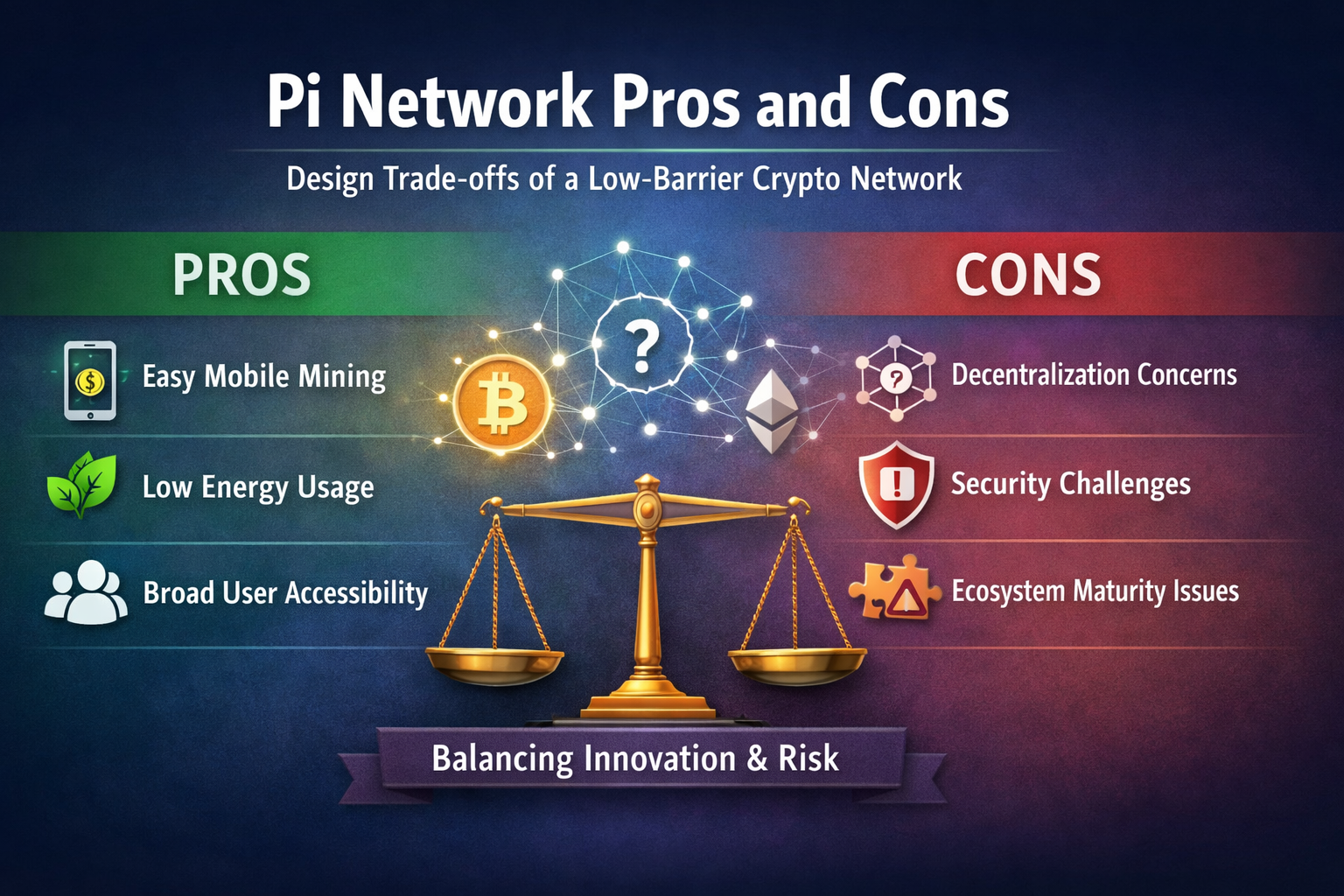
Pi Network Pros and Cons: Design Trade-offs of a Low-Barrier Crypto Network
The controversy surrounding Pi Network is not simply a matter of whether it is good or bad. At its core, it reflects different trade-offs in design goals and development paths across crypto networks. Understanding the strengths and limitations of Pi Network helps place it within the broader crypto landscape, rather than judging it solely by the standards used for traditional mining networks.
The Original Design Intentions of Pi Network
Pi Network emerged from a reassessment of how early crypto networks structured participation.
In proof-of-work (PoW) networks such as Bitcoin, mining gradually became a highly specialized and capital-intensive activity. As computing power consolidated and energy consumption increased, the space for ordinary users to participate in blockchain networks continued to shrink.
Pi Network was not designed to replicate the model of hash power competition. Instead, it attempts to address several core questions:
How can more non-technical users participate in crypto networks?
How can a network operate without relying on energy-intensive hardware?
How can network scale be achieved quickly in the early stages?
For this reason, its design prioritizes participation, usability, and network expansion speed over achieving maximum decentralization from day one.
What Are the Main Advantages of Pi Network?
Significantly Lower Participation Barriers
Participating in Pi Network does not require running complex nodes or configuring professional mining equipment.
Users primarily engage through periodic actions on a mobile device, a relatively uncommon model in the crypto space.
A low barrier to entry does not mean low technical sophistication. Rather, it reflects a deliberate design choice tailored to a broader user base, with the direct effect of expanding the pool of potential participants.
More Manageable Resource Consumption
Unlike networks that depend on continuous computational competition, Pi Network does not require sustained high-intensity processing. This reduces reliance on energy and specialized hardware, and lowers the hidden costs of participation.
Emphasis on Identity and Social Relations
Pi Network introduces concepts such as “trust circles,” attempting to incorporate social relationships into network security and incentive distribution. This approach differs noticeably from fully anonymous, hash power–driven security models.
Lower Cognitive Barrier for Users
Its participation logic is relatively intuitive, which helps new users understand how a crypto network functions. From an educational and adoption standpoint, this offers a distinct advantage.
Major Controversies and Limitations Facing Pi Network
Decentralization Still in Progress
In its early stages, Pi Network relied heavily on its core team and node structure. As a result, it is often compared with mature networks such as Bitcoin in terms of decentralization.
However, such comparisons often overlook differences in development stage and design objectives.
Security Model Requires Long-Term Validation
Reducing reliance on hash power competition lowers resource consumption, but it also means other mechanisms must sustain network security.
Models based on identity and social relationships may, in theory, be susceptible to manipulation or concentrated influence. Their real-world resistance to attack can only be assessed through long-term operation.
Sustainability of Incentive Mechanisms
When participation costs are low and user numbers expand rapidly, maintaining an effective incentive structure becomes a structural challenge that Pi Network must continue to address.
Pi Network vs Other Crypto Networks: A Comparative View
When comparing Pi Network with other mainstream crypto networks, one premise must be clear: different networks are designed to solve different problems, so evaluation standards should not be identical.
Differences in Design Objectives
Bitcoin aims to build a highly secure, censorship-resistant value transfer system. Security and decentralization are its top priorities.
Ethereum emphasizes general-purpose computation and smart contract functionality, balancing security, performance, and scalability.
By contrast, Pi Network focuses more on broad participation and rapid network expansion, seeking to make crypto networks accessible beyond a narrow technical community.
Security Mechanisms and Cost Structures
Bitcoin increases the cost of attack through hash power competition, a model that comes with high energy consumption.
Pi Network relies more on institutional design, identity systems, and network rules to maintain order, with costs reflected in governance complexity rather than electricity usage.
Paths Toward Decentralization
In Bitcoin, decentralization emerged organically as nodes and miners distributed globally.
In Pi Network, decentralization depends more on phased planning and adjustments to node structure, reflecting a more design-driven evolution path.
Comparative Summary at the Structural Level
| Dimension | Pi Network | Bitcoin |
| Core Objective | Broad participation and accessibility | Security and censorship resistance |
| Participation Barrier | Low | High |
| Security Model | Mechanism and identity-based support | Hash power competition |
| Energy Consumption | Relatively low | Relatively high |
| Path to Decentralization | Planned development plus gradual evolution | Organic competition-driven formation |
The differences between Pi and Bitcoin do not represent a simple hierarchy of superiority or inferiority. Instead, they reflect distinct answers to the question of who a crypto network is ultimately meant to serve.
Evaluating Pi Network from the Perspective of Security and Decentralization
In blockchain system design, security, decentralization, and efficiency are difficult to maximize simultaneously.
Pi Network’s approach leans more toward efficiency and breadth of participation. This implies:
Security is maintained primarily through institutional design and network rules.
Decentralization advances progressively as the network evolves.
Network stability depends on long-term governance capability.
Such a structure is better suited to gradual development rather than instant completion.
Challenges from an Ecosystem Development Perspective
User scale does not automatically translate into a mature ecosystem.
At the ecosystem level, Pi Network must address issues such as:
Real demand for practical application scenarios
Developer willingness to participate and tool maturity
Transparency and predictability of network rules
Ecosystem development often lags behind user growth, and its effectiveness typically becomes visible only over time.
How to Rationally Assess the Pros and Cons of Pi Network
A balanced assessment requires placing Pi Network within the appropriate comparative framework.
It is not a replacement for Bitcoin, but rather an experimental crypto network aimed at a broader user base.
Its strengths and limitations arise from the same underlying design logic, not from isolated circumstances.
Conclusion
Pi Network’s low-barrier design expands the boundaries of participation in crypto networks, while also introducing ongoing discussions about security, decentralization, and ecosystem maturity.
Understanding these trade-offs helps situate Pi Network within the broader crypto system from a structural design perspective, rather than evaluating it by a single standard.
FAQ
Q1: Is Pi Network fully decentralized? Its level of decentralization remains in development and continues to depend on the evolution of network structure and node distribution.
Q2: How is Pi Network’s security maintained? Its security model emphasizes identity systems and institutional mechanisms rather than pure hash power competition, and its effectiveness requires long-term validation.
Q3: What is Pi Network’s core innovation? Its primary innovation lies in expanding the user base of crypto networks through a low-barrier participation model.
Related Articles

What is Fartcoin? All You Need to Know About FARTCOIN
Gold Price Forecast for the Next Five Years: 2026–2030 Trend Outlook and Investment Implications, Could It Reach $6,000?
2026 Silver Price Forecast: Bull Market Continuation or High-Level Pullback? In-Depth Analysis of Silver Candlestick Chart

Crypto Future Profit Calculator: How to Calculate Your Potential Gains

Crypto Futures Calculator: Easily Estimate Your Profits & Risks


